Latest Posts
![[Outlook] How an attacker could modify your sent items!](/assets/img/blog/outlook_banner.jpg)
[Outlook] How an attacker could modify your sent items!
In the world of business disputes, the "Sent Items" folder is often treated as the source of truth. We implicitly trust that what sits in that folder is...

Crafting Malicious Facebook Ads via Instant Experiences
Everyone who uses Facebook has seen them: slick, fast-loading ads that open up into a full-screen experience without ever leaving the app. These are...

Bypass client-side validation on a Facebook Page Contact Form
The "Action Button" feature found against a Facebook page has an option to create a Contact Form. This Contact Form allows a page to collect...
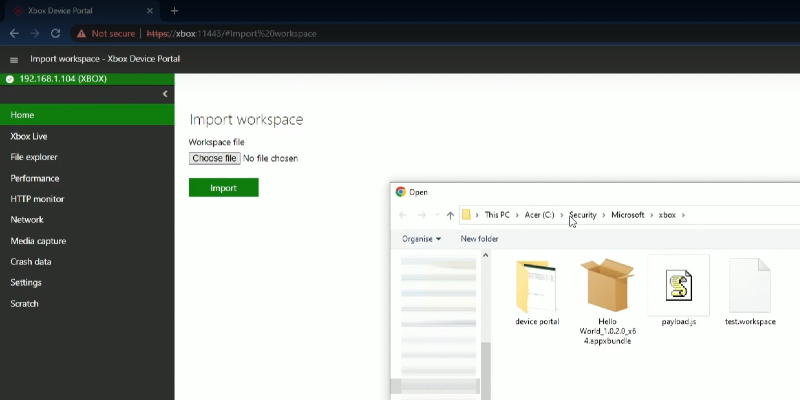
XSS to RCE - Xbox Device Portal
The Xbox Device Portal is an invaluable tool for developers, offering remote access to an Xbox console in developer mode via a web browser. It allows...

Bountycon 2022 - Android Trinity PWN
Whilst working on the BountyCon 2022 CTF, I spent the majority of the time focusing on the Android Trinity challenge. This was one of two PWN...

Disclosing BCC Recipients of an email
This post will cover an interesting logic flaw found in a private bug bounty program. Whilst the name of this company will be known as...